Over the past few years there has been a significant increase in bot attacks on companys’ email lists, including new takes on an old classic.
Traditional bot attacks on an email list targeted a company. More specifically, a bot would be pointed at a company sign up form and generate thousands of fake email addresses to flood the business’ lists with bad data. Mailing to a large number of bogus addresses (especially if they were any of the major ISPS i.e.: bogus1@gmail.com) could hurt email delivery by causing a spike in unknown addresses, leading to filtering.
These attacks used to be fairly simplistic and the bogus addresses were easily recognizable when skimming through a list of questionable signups. They usually consisted of a string of random or incrementing letters and numbers and generally stood out compared to legitimate addresses.
1212967@gmail.com
121873@gmail.com
g205072@gmail.com
If any additional information was needed to submit the form (e.g. First Name, Last Name) then you could usually identify a bot from those fields as well by a string of random characters.
Other ways of identifying the bot addresses would be to check the IP address the sign up came from. If you see multiple hundreds or thousands of sign ups from a single IP address, it’s a good bet you were targeted by a bot. Bots did get more sophisticated over time, by either utilizing more “genuine looking” email address generators or by randomizing the IPs used for sign ups.
List Bombing
However, a new type of bot attack has appeared with increasing frequency (and complexity), known as “list bombing”. It differs from a traditional bot attack in that instead of targeting a company, they are actually targeting the subscriber. List bombing consists of signing up legitimate email addresses to hundreds or even thousands of different mailing lists, creating what amounts to a DDOS attack of the user’s inbox.
These attacks use legitimate companies mail programs to render an individual’s inbox unusable. With new messages coming in potentially as fast as every 2-3 seconds, there is no way someone could filter through to find the mail they need.
From a company perspective, these types of attacks can be much harder to identify. Unless a particular bot signs up a large number of addresses at once or in a short time all from the same IP, these addresses are legitimate and wouldn’t stand out in a list of recent sign ups like fake ones would. Also, being that they are real functioning addresses, they don’t bounce either.
Your mail program could be getting hijacked to harass and abuse people and you might not even know it.
Initially these types of attacks were used against various government addresses, but over time also targeted specific members of the anti-spam community as well as others. This led Spamhaus to begin listing the IP addresses of companies whose forms were being used as part of these attacks. So completely legitimate companies were suddenly getting hit with the biggest of blacklists, pretty much without warning. Hackers even started selling list bombing as a service. You could go to a website and pay $75 to have a particular email address targeted with list bombing.
Of course, you don’t want your mail program caught up in all of these shenanigans, so what can you do about it?
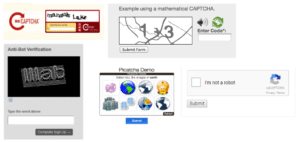
Captchas
In terms of prevention, placing a captcha on your sign-up form is the best way to help deter bots. There are many different types of captchas, some require clicking on pictures, typing the words/numbers from a set of fuzzy images or solving a simple math equation.
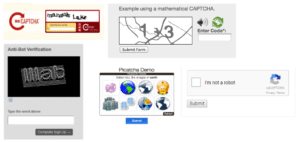
A captcha works under the assumption that bots won’t be able to read a picture or solve an equation the way an actual human being would. However, these captchas can be very frustrating for a subscriber (hard to read, complicated, etc.) which is one of the reasons certain companies chose not to utilize them in the past.
The last example (see image above), the checkbox with “I am not a robot”, shows how far captchas have come over the years. Google’s “NoCaptcha ReCaptcha”, from a subscriber’s perspective, only requires them to click on the checkbox and still performs the function of preventing bots from making submissions.
Double Opt-In
Setting up double opt-in (DOI) is another step you can take to help mitigate bot attacks and list bombing. DOI triggers a confirmation email to the address after a sign up asking the user to confirm that they intended to receive mail from you. If the user clicks the confirm link in the email, they get added to your lists, if they don’t, then they get suppressed going forward.
So, whether someone fat fingers their address when signing up or gets targeted by a bot, unintended recipients will only ever receive that initial message from you, unless they take the additional step to verify the sign up.
While DOI by itself will not prevent a bot attack from using you to target some poor innocent address (hundreds or thousands of confirmation emails still causes the same issues as that many regular messages for the end user and their inbox), it will help to ensure that these attacked addresses never make it over to your main lists.
In this way, it minimizes the long-term impact of an attack on both you and the intended target. Additionally, DOI is considered a best practice for sign up hygiene and is also the gold standard for proving explicit consent in light of GDPR and future regulations. Even if someone entered the wrong address at sign up, DOI proves you are taking diligent and active steps to avoid sending spam.
Wrap Up
As captchas have gotten more user friendly and bot attacks have increased, there really isn’t a reason not to implement one and protect your signup forms and mailing lists at their source.
Setting up captchas on all your sign-up forms before you become a target or are used to target someone else can help you avoid a costly blacklisting, as well as save you the headaches and man-hours spent digging into lists to find when an attack began, how long it went on for, etc.
Additionally, it can prevent you from losing legitimate signups, as many times clients find they need to throw away entire days or weeks’ worth of sign ups just to ensure they had truly gotten rid of all bad data from the window of an attack (having DOI in place would also negate this painful part of being used in a list bombing attack).
Of course, we recommend setting up both captcha and DOI, bringing your email program that much closer to being best in class.
 Blog
Blog Resources
Resources Learning
Learning About us
About us